Reminder: Compliance Does Not Equal Security

This article was originally posted on the AFSA Blog.
When two things are closely related, we tend to trick ourselves into thinking the two are interchangeable. Wash your hands and you won’t get sick. Smile often and people will like you. Pass your PCI Compliance audit and your customers’ data is safe.
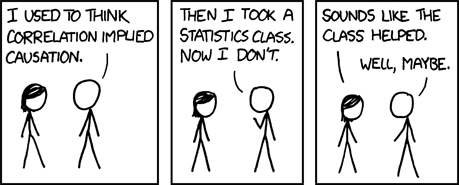
This common fallacy is formally known as “cum hoc ergo propter hoc”, but you’re likely more familiar with its English counterpart: Correlation doesn’t imply causation. In some cases, it’s painfully obvious when this is at play, like how the declining divorce rate in Maine has a 99.6% correlation with the decline in consumption of margarine (we finally believe it’s not butter!)

Other times, the relationship between two concepts is so intertwined that we struggle to identify the fallacy. For businesses who collect card payments from customers, there is significant danger in assuming that PCI compliance and data security share a causal relationship.
Finding the Gaps
While we won’t get too deep into the gaps between data security and PCI-DSS compliance (two extremely complex and nuanced topics), it’s important to examine a few of the areas where the two diverge.
Compliance Addresses Risks, Not Threats
Those familiar with PCI-DSS know that compliance is split into different levels based roughly on the number of card transactions you process. Level 1 businesses, who process more than 6 million card transactions annually, have much more rigorous requirements to adhere to than their Level 4 counterparts, who handle a significantly lower number of transactions.

But do security threats subdue themselves when dealing with smaller merchants? No. The same threats that can be difficult for an L1 to fend off may be exponentially more difficult for a L3 or L4 merchant to handle. The big bad wolf will blow just as hard, regardless of whether your house is made of brick or straw, and the fines can be equally high for merchants in any tier.
Compliance Can’t Cover Everything
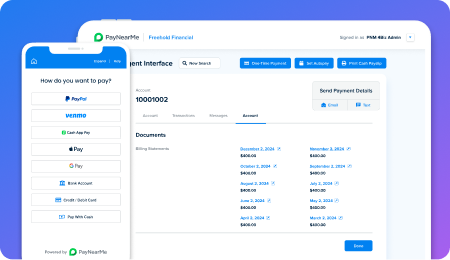
In a recent webinar with PayNearMe and AFSA, we shared three examples of organizations that were PCI compliant but still suffered massive data breaches. The reasons may surprise you, but they can happen to any business.
- Vendors: Are all of your vendors practicing data security best practices? What about their vendors? Are they even PCI-DSS compliant?
- Technology: Does your technology put you at risk for a breach? Are there backdoors between internal systems that could cause issues?
- Employees: Are there mechanisms in place to ensure your employees don’t abuse or misuse customer data?
This list is far from comprehensive, but illustrates an important consideration for your team: being 100% compliant does not necessarily make you secure.
Compliance Isn’t Realtime
While compliance standards are changing all the time, they don’t adapt in real time. Looking at the current PCI-DSS standards, this becomes clear. Many of the standards are months or even years old – and for good reason. Compliance standards must balance constant evolution with fixed intervals to ensure organizations actually know what to adhere to.
Large organizations, especially Level 1 & 2, go through rigorous audits and large scale process reviews to meet PCI compliance standards. It would be nearly impossible to change standards without ample time for organizations to adapt.
Data security must be more proactive (and reactive) to real-time threats in the environment. If a vicious piece of malware or a third party software exploit is making its way through the web, companies cannot afford to wait for a new standard.
Again, compliance does not equal security.
Don’t Lose Sight of What’s Important
It’s worth circling back to reiterate a critical point: compliance is still extremely important. It provides a measuring stick for how well you are doing in critical security areas, identified by some of the most influential leaders in card processing and infosec.
As a business, you should look at proper PCI compliance as one path to the end goal of data security, but not the only one. Security is a strategy, an ongoing framework to protect customer data. Compliance is a thoughtful standard to guide you there.
Forever linked, but not the same.